Secure IT Infrastructure 631679524 Online

The concept of secure IT infrastructure is critical in today’s digital landscape. Organizations face increasing threats to their sensitive data and operational integrity. A comprehensive security framework must incorporate stringent protocols, continuous monitoring, and employee training. The effectiveness of these measures hinges on understanding key components and best practices. However, as cyber threats evolve, organizations must remain vigilant and adaptable. What strategies can be employed to ensure resilience against these persistent challenges?
Understanding the Fundamentals of Secure IT Infrastructure
Understanding the fundamentals of secure IT infrastructure requires a comprehensive analysis of various components that contribute to its integrity and resilience.
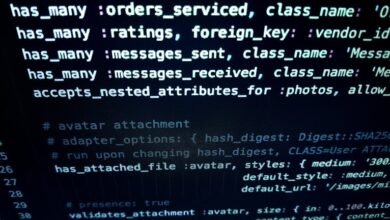
Key elements include the implementation of robust security protocols, which safeguard data transmission, and effective network segmentation, which limits potential attack surfaces.
These measures collectively fortify the infrastructure, ensuring operational continuity while promoting a secure environment that upholds the principles of freedom and privacy for users.
Key Components of a Robust IT Security Framework
Although various factors contribute to a secure IT environment, a robust IT security framework is fundamentally anchored in several key components.
Central to this framework are comprehensive risk assessments that identify vulnerabilities, alongside stringent security protocols designed to mitigate identified risks.
These elements work in concert to establish a resilient infrastructure, empowering organizations to maintain autonomy while safeguarding sensitive data against evolving threats.
Best Practices for Maintaining IT Infrastructure Security Online
Maintaining IT infrastructure security online requires a strategic approach built upon the foundation of a robust security framework.
Regular security audits are essential for identifying vulnerabilities, while an effective incident response plan ensures rapid containment and mitigation of threats.
Tools and Technologies to Enhance Your IT Security Posture
A comprehensive array of tools and technologies exists to bolster an organization’s IT security posture, each designed to address specific vulnerabilities and enhance overall defense mechanisms.
Security automation facilitates streamlined responses to incidents, while threat intelligence provides actionable insights that inform proactive measures.
Together, these elements create a robust framework, empowering organizations to effectively mitigate risks and maintain operational integrity in an ever-evolving threat landscape.
Conclusion
In conclusion, the significance of a secure IT infrastructure cannot be overstated, particularly as cyber threats continue to evolve. Notably, a report by Cybersecurity Ventures predicts that global cybercrime costs will reach $10.5 trillion annually by 2025, underscoring the urgency for organizations to adopt robust security frameworks. By implementing best practices, utilizing advanced tools, and fostering a security-aware culture, organizations can effectively mitigate risks and safeguard their sensitive data against potential breaches.