Secure IT Infrastructure 120839046 Online

A secure IT infrastructure is essential for protecting sensitive information and ensuring operational continuity. Organizations must implement robust security measures, including stringent access controls and effective network segmentation. Evaluating existing security protocols is critical to identify vulnerabilities. As cyber threats evolve, adapting to emerging trends in IT security becomes imperative. The effectiveness of these strategies can significantly influence organizational resilience and growth in an increasingly digital landscape. What measures should be prioritized to enhance security further?
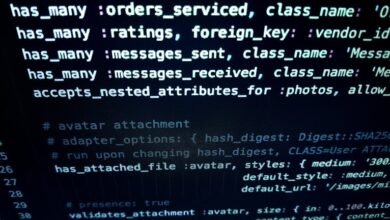
The Building Blocks of a Secure IT Infrastructure
While organizations increasingly rely on digital solutions, establishing a secure IT infrastructure remains paramount to safeguarding sensitive data and maintaining operational integrity.
Fundamental elements include robust access controls that ensure only authorized users can access critical systems, alongside effective network segmentation, which isolates sensitive data from broader networks.
Together, these building blocks create a resilient framework, supporting organizational freedom while mitigating security vulnerabilities.
Top Cybersecurity Measures to Implement
As organizations navigate the complexities of the digital landscape, implementing robust cybersecurity measures becomes essential for protecting sensitive information and maintaining operational continuity.
Key strategies include network segmentation to limit access and minimize potential breaches, alongside leveraging threat intelligence for proactive defense.
How to Evaluate Your Current Security Protocols?
How can organizations systematically assess their current security protocols to identify vulnerabilities?
Conducting a comprehensive security audit is essential, integrating thorough risk assessments to pinpoint weaknesses. This process involves evaluating existing safeguards, analyzing potential threats, and prioritizing areas for improvement.
Future Trends in IT Security You Should Know About
Emerging trends in IT security are poised to reshape the landscape of organizational defense mechanisms, as advancements in technology and evolving threat vectors necessitate a proactive approach.
AI advancements will enhance threat detection and response capabilities, while cloud security innovations will address vulnerabilities inherent in remote infrastructure.
These developments underscore the need for adaptive strategies that prioritize resilience and autonomy in the face of increasingly sophisticated cyber threats.
Conclusion
In an era where cyber threats lurk around every digital corner, the importance of a secure IT infrastructure cannot be overstated. Organizations that fail to prioritize rigorous security measures may as well be inviting cybercriminals to a lavish banquet of sensitive data. By bolstering access controls, employing network segmentation, and embracing cutting-edge innovations, companies can fortify their defenses and ensure not just survival, but thriving amidst chaos. Thus, the choice is clear: invest in security or risk catastrophic consequences.